Only two versions of the TLS (Transport Layer Security) protocol can be considered safe under certain circumstances: TLS 1.3 and TLS 1.2. Trying to get your bank alongside everyone else to fix their websites and web applications is a Herculean task; good luck trying. Even so, you can protect TLS connections by modifying the browser configuration.
It is good to know that there is something you can do to protect at least yourself and the other end users on the networks that you oversee from nasty attacks against their TLS connections. In Firefox, you can restrict the browser to “speak” only TLS 1.3 and TLS 1.2 to limit the attack surface and restrict phishing. Here is how to do it.
Here is a short how-to on restricting Firefox to the two most secure versions of the TLS protocol:
Step 1. Open the advanced settings page of Firefox.
In the address bar, enter
about:config
and hit Return.
Step 2. Agree to “void your warranty”.
Ignore the warning about voiding your warranty and proceed.
Step 3. Find the security settings for TLS
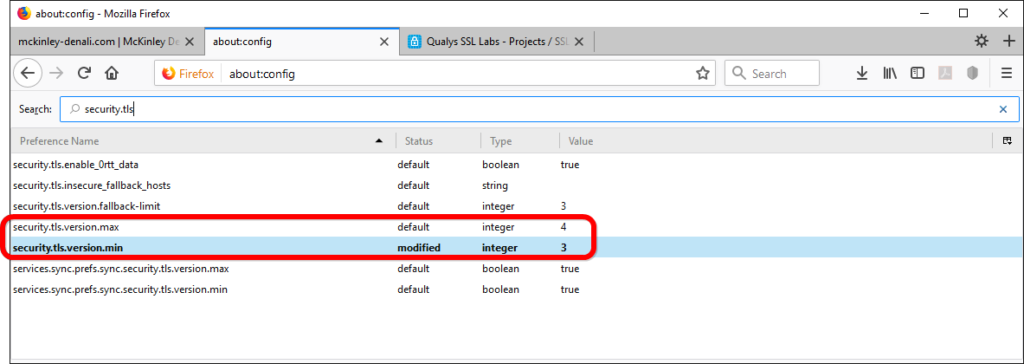
In the Search bar, type in “security.tls”.
Step 4. Adjust the lowest version of the TLS protocol you want to allow
Double click the entry “security.tls.version.min”. The default value is 1. Change it from “1” to “3”. This will activate TLS 1.2 and disallow any version below. This change is important as it prevents protocol downgrade attacks irrespective of the actual server settings. Eliminating the possibility of a protocol downgrade allows you to protect TLS connections from some attempts at eavesdropping.
Step 5. Adjust the highest version of the TLS protocol you want to allow
Verify that “security.tls.version.max” is set to to “4”. This ensures that Firefox may use TLS 1.3, (but not above; should TLS reach a higher version number, you will need to revisit this setting).
Now, your Firefox web browser speaks only TLS 1.3 and TLS 1.2; you will not be able to connect to websites that do not support these two protocols, but then again—perhaps you shouldn’t. Either way, there aren’t that many of them left.
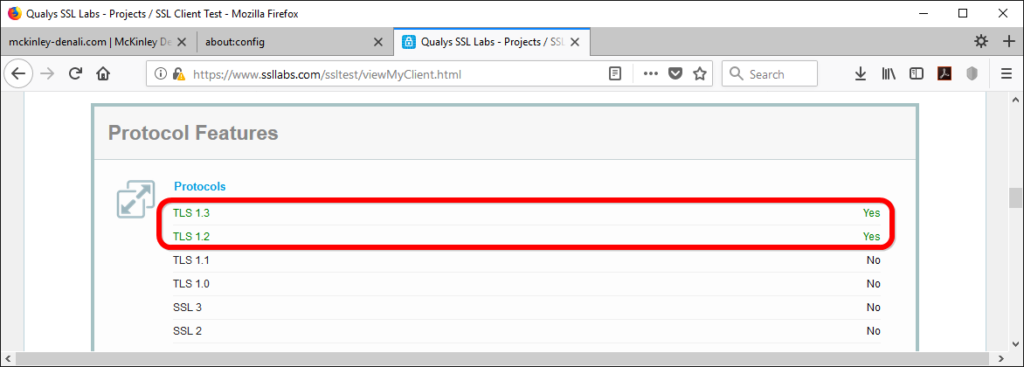
Step 6. Test your configuration
Head over to Qualys SSL Labs’ browser test:
https://www.ssllabs.com/ssltest/viewMyClient.html
Step 7. Verify the test results
Allow the test to run its course. In the overview of details, look for the section “Protocol Features”. In the list of supported protocols, verify that only TLS 1.3 and TLS 1.2 are allowed.
These changes do not offer absolute security as such a thing doesn’t even exist. They offer protection in so far as they limit the attack surface without compromising compatibility.
It goes without saying that if you happen to oversee the configuration of a web host, you need to take some steps to ensure that it measures up to the demands you put on your own Firefox for the sake of your visitor’s safety (see “How to Activate HTTP/2 with TLS 1.3 Encryption in NGINX for Secure Connections without a Performance Penalty” and “TLS 1.3 (with AEAD) and TLS 1.2 cipher suites demystified: how to pick your ciphers wisely” for more).
Leave a Reply