In the age of cyber warfare, being paranoid is the only reasonable attitude and that means, among other things, being paranoid about software updates.
Take for example OpenSSL. This open source cryptography library that implements the Transport Layer Security (TLS) and Secure Sockets Layer (SSL) protocols is designed to “secure communications over computer networks against eavesdropping”, but guess what: it has been riddled with bugs since its inception. This may be unavoidable, to a certain degree — after all, we are speaking about software. Even so, the inherent flaws of OpenSSL should not be an excuse for not keeping the version you use as bullet-proof as possible. Let’s not forget that your car is most likely hackable by a 15 year old and yet you still (presumably) lock the doors.
While you can’t do much about the yet-to-be-identified bugs, you can at least protect your systems from those bugs that have been already patched up and widely documented.
Too bad the official OpenSSL website offers Linux sources only.
While Linux distributions routinely come loaded with OpenSSL, this is not the case for Windows… or shall we say “Windows distributions”. (Didn’t Microsoft want to “Linuxify” its flaggship OS? Never mind.) If you want to run it, you need a Windows binary, and unless you are willing to compile it yourself, you have to to rely on someone else.
Here is how you can set up OpenSSL on Windows without having to deal with the code.
Step 1. Get hold of the binaries
Finding Windows binaries of OpenSSL is not an easy task, but don’t get discouraged. They do exist. To download them, navigate to:
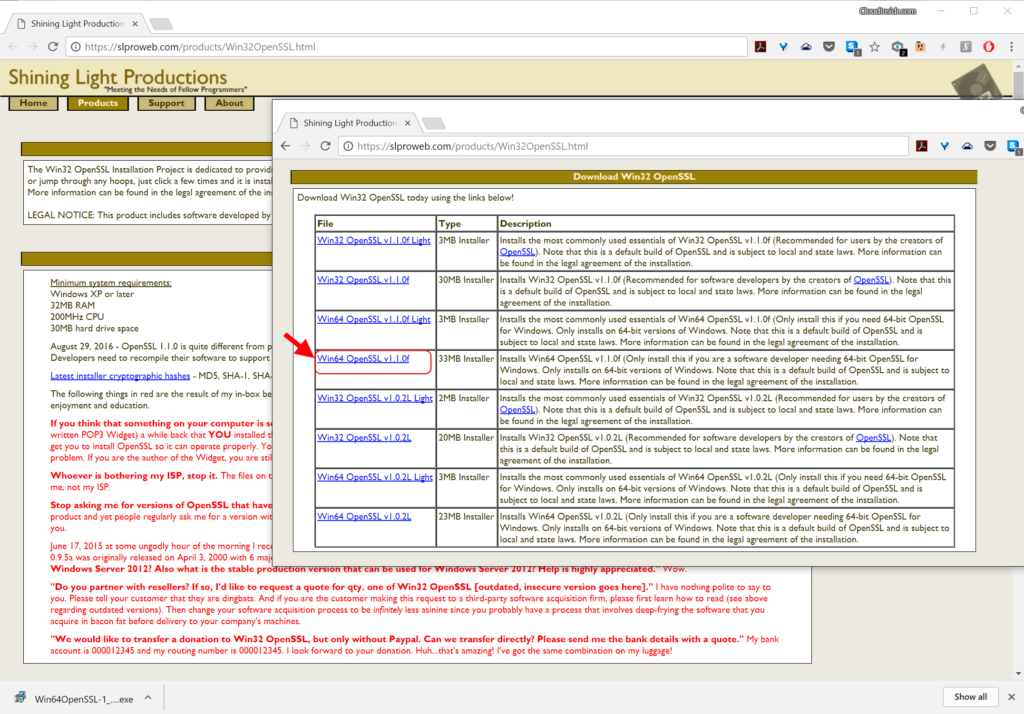
https://slproweb.com/products/Win32OpenSSL.html
Don’t be fooled by the Win32 string in the URL nor by the navigation pointing you to a seemingly ancient download page from way back in 2004 (from the “Products” tab through the “Win32 OpenSSL link”). Scroll down the page to the section “Download Win32 OpenSSL”, ignoring the confusing string. Now you need to pick the right binary from the list. For each version, there are two basic types: the full installer and the light installer.
Download the one named “Win64 OpenSSL v1.1.0f” (or a higher-numbered version once it becomes available) to get the full installer.
The current version as of this writing (OpenSSL 1.1.0h) is very different from previous releases. It is not the same thing at all so pay attention to the release numbers! The worst thing you can do is use an old version that has documented bugs that anyone could exploit following a howto!
Step 2. Run the installer
We recommend installing OpenSSL outside of your Windows system directory.
Step 3. Start the OpenSSL binary
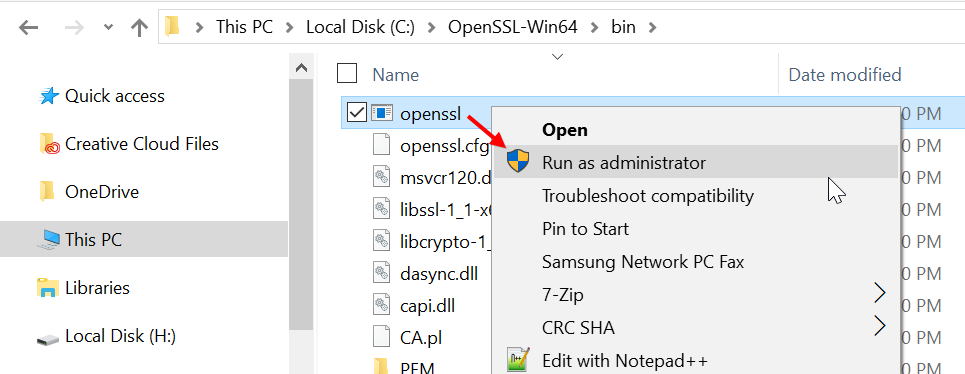
To invoke OpenSSL, you can simply right-click on it in the Windows Explorer at its install location, for example in:
C:\OpenSSL-Win64\bin\
then choose “Run as Administrator”.
It will open a cmd window with the OpenSSL command prompt. Here is what to expect.

Now you are ready to start creating your OpenSSL keys. (Speaking of which: users of the remote access utility PuTTY can export an OpenSSH key from PuTTYgen.) When using OpenSSL on Windows in this way, you simply omit the openssl command you see at the prompt. For example, to generate your key pair using OpenSSL on Windows, you may enter:
openssl req -newkey rsa:2048 -nodes -keyout key.pem -x509 -days 365 -out certificate.pem
and follow the onscreen instructions as usual. To review the certificate:
openssl x509 -text -noout -in certificate.pem
and so forth.

Leave a Reply