Until the day TLS 1.3 becomes widely supported, web servers must rely on a fallback to TLS 1.2 with correctly configured server directives and strong cipher suites. Pick the wrong settings and you declare an open season on your server.

Cyber security, infotech

Until the day TLS 1.3 becomes widely supported, web servers must rely on a fallback to TLS 1.2 with correctly configured server directives and strong cipher suites. Pick the wrong settings and you declare an open season on your server.

Confused about SSL/TLS certificates? Here is a quick and dirty introduction to SSL/TLS encryption.
[Updated May 16, 2018] AWS and Microsoft, the two leaders in the race for the best cloud infrastructure, have recognized cyber security as a barrier of adoption. Cyber security professionals are weary of migrating workloads into public cloud environments as it may carry significant risks. Thus, Amazon and Microsoft have developed specialized services to help safeguard users’ cloud infrastructure and data.
This post discusses ways to mitigate cyber threats and launch a cyber defense on AWS and Azure.

In order to figure out how many days your letsencrypt certificates have left, you could check an online services such as:
https://www.ssllabs.com/ssltest/index.html
However, that won’t work for a mail server that’s not also running a web server using the same certificate.
In this case, your best bet is to check the certificate file directly using the openssl command as follows:
openssl x509 -noout -dates -in /etc/letsencrypt/live/smtp.yourmailserverdomainname.com/cert.pem
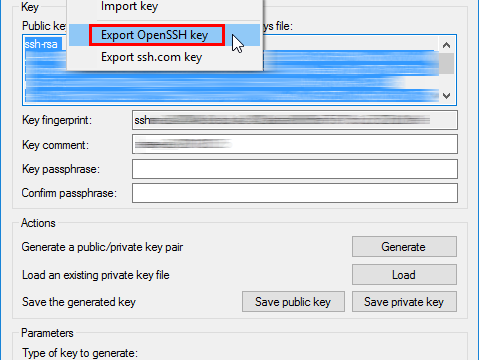
When using authentication based on keys (as opposed to a password), you have to create the key pair—a private key and a public key—on your local machine, then transfer the public key to the server and install it there. Here is how to do this on a Windows desktop for remote access to a Linux server.
©2022 CybrAnalytiqa OÜ