[Updated May 16, 2018] AWS and Microsoft, the two leaders in the race for the best cloud infrastructure, have recognized cyber security as a barrier of adoption. Cyber security professionals are weary of migrating workloads into public cloud environments as it may carry significant risks. Thus, Amazon and Microsoft have developed specialized services to help safeguard users’ cloud infrastructure and data.
This post discusses ways to mitigate cyber threats and launch a cyber defense on AWS and Azure.
AWS and Microsoft have each developed a wide array of security-related services, spanning from key management to organization management and anything in between.
There is no question that cyber security in any IT environment rests on proper access governance and authorization management—thoghtfully architected and thoroughly enforced.
Authenticate and authorize: AWS IAM and Azure AD
Cyber security—in any IT environment—starts with enforcing bullet-proof authentication and authorization. This is nowhere as important as in an Anything-as-a-Service deployment scenario.
AWS Identity and Access Management
The service IAM (short for Identity and Access Management) allows you to create users and groups and to control their access to resources at the cloud level. This functionality is independent of your control of system-level access to individual compute instances, databases or other services.
Instead of creating IAM users in your AWS account, you can also manage user identities outside of AWS and control their access to your AWS resources from within the IAM service. For example, your AWS users could log in to with their Amazon, Facebook or Google identities. This functionality requires you to configure your external authentication services as identity providers (IdP) in IAM. This will establish a trust relationship between your AWS account and the external IdP. This is called identity federation.
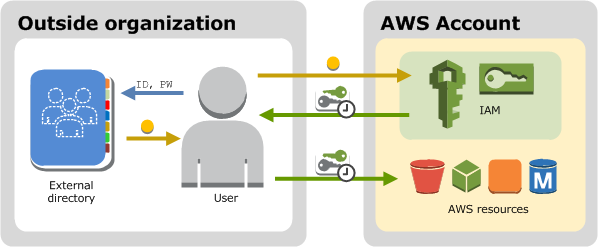
AWS supports two standards of identity federation:
- Web Identity Federation using OpenID Connect (OIDC), including Amazon’s own service AWS Cognito (this is the recommended scenario to authenticate users in mobile apps using temporary AWS credentials issued upon request by the federated service)
- SAML 2.0-based Federation (Security Assertion Markup Language 2.0), including: Microsoft’s Active Directory Federation Services and open-source Shibboleth (no need to write code; the AWS Management Console will suffice).
Azure Active Directory (versus Microsoft Active Directory)
The equivalent in Microsoft’s cloud is called Azure Active Directory. It is not the same thing as Microsoft Active Directory!
Azure Active Directory allows you to create and manage users and groups and to allow and deny access to particular resources of the Azure environment. Microsoft AD is confined to systems.
Azure AD, on the other hand, is a multi-tenant identity and management system that underpins the entire Microsoft cloud. It’s huge. It even provides a single sign-on for 3rd-party SaaS applications. This powerful feature is implemented either through federation (whenever supported by the application) or through password vaulting and form-based authentication (when federation is not supported).
Active Directory Federation Services (AD Federation Services or AD FS for short) is a feature in Windows Server which extends single sign-on access of individual users to external applications and systems.
Microsoft’s Active Directory (AD) service for Windows Server workloads integrates with AWS Directory Service for Microsoft AD on AWS. The latter one supports CloudTrail logging within AWS. How nice.
Identify B2C customers with Azure Active Directory B2C
With its Azure Active Directory B2C, Microsoft has developed a unique offering for cloud-based customer identity and access management. It is a global identity management service for consumer-facing applications. It offers high availability and scales to hundreds of millions of identities.
Multi-Factor Authentication
Both AWS IAM and Microsoft Azure AD support Multi-Factor Authentication (MFA) with a variety of verification methods such as token generators in hardware, mobile apps, phone calls and text messages. It should go without saying that MFA should be enabled on every cloud user’s account.
Hand out the keys: AWS KMS and CloudHSM versus Azure Key Vault
Passwords are a thing of the past. These days, authentication for the use of cloud services requires key pairs. Since cryptographic keys cannot be memorized (nor is it practical to type them in from post-it notes), they must be managed digitally and in a secure manner. In other words, unless you secure your private keys in a iron-clad manner, you leave the doors wide open to intruders.
AWS Key Management Service and CloudHSM
With its Key Management Service (AWS KMS for short), AWS allows you to get a grip on the multitude of encryption keys required to work with its services and your systems.
KMS is a fully managed service. To protect the security of your keys, KMS uses Hardened Security Appliances (NOT to be confused with Hardware Security Modules; the latter ones would be made by a third-party vendor, the former ones are built by Amazon, then certified). Amazon manages these appliances for you.
KMS integrates with AWS CloudTrail for logging and auditing, a dream come true in terms of regulatory compliance. The entire security information and event management (SIEM) market is based on log management. CloudTrail comes in handy.
With AWS CloudHSM, you get a dedicated access to a managed hardware security module (HSM) in the network isolation of a VPC (Virtual Provate Cloud). Dedicated means you do not share the HSM device with anyone. Only you control access to your keys as verified by 3rd parties — unlike with KMS where AWS gets a say.
As an alternative, AWS offers you the ability to Bring Your Own License (BYOL for short) or purchase additional security software on the AWS Marketplace.
Microsoft Key Vault
On Microsoft Azure, key management comes down to using Key Vault. It provides a way to manage, create, and control encryption keys stored in FIPS 140-2 Level 2 validated HSMs (hardware security modules) on Azure. It will also safeguard your infrastructure’s other secrets.
Data encryption on AWS and Microsoft Azure
Data encryption comes in many shapes and forms.
Encrypt data at rest
When it comes to encryption of data at rest, AWS and Azure sport very similar abilities.
When using AWS services such as S3, Glacier, EBS, RedShift, RDS, DynamoDB and others, you can either:
- create and manage your own keys off the cloud and transfer only your already encrypted data to AWS (client-side encryption), or
- create your keys off the cloud and transfer only already encrypted data to the cloud (client-side encryption), but at the same time manage your keys in the AWS Cloud using either KMS or CloudHSM, or
- allow AWS to create and manage the keys for you and also to encrypt your data with your keys in the cloud; this concept is called server-side encryption.
AWS supports server-side encryption for data on S3 and EBS data volumes as well as Elastic File System (EFS). AWS encrypts data transparently while it is being written, and transparently decrypts it while it is being read, eliminating the need to modify existing applications.
Similarly, Microsoft’s Azure Storage Service Encryption (SSE) encrypts your data prior to persisting it to Azure Storage, Azure Blob Storage and File Storage, and it decrypts the data prior to retrieval.
Related: How to Restore Your Instance Data from a Backup using Snapshots on AWS EC2/EBS.
Encrypt data in transit
To ensure the security of data in transit, Secure Sockets Layer/Transport Layer Security (SSL/TLS) certificates come into play. They serve a twofold purpose. They are believed to secure network communications and they can establish the identity of the party presenting the certificate (for more on how this works, read A quick introduction to SSL/TLS encryption: understanding certificates and key pairs).
However, purchasing, uploading, and renewing SSL/TLS certificates can be time consuming and also costly. Enter AWS Certificate Manager.
AWS Certificate Manager
AWS Certificate Manager lets you provision, manage, and deploy Secure Sockets Layer/Transport Layer Security (SSL/TLS) certificates on AWS without paying a dime. (It is worth noting that you do pay for the other resources you consume to keep your application humming.)
Azure App Service
The App Service platform by Microsoft supports SSL bindings for custom hostnames. These require a PFX certificate (.pfx). In partnership with GoDaddy, Microsoft has introduced App Service Certificate (ASC), a certificate service for App Service customers available in the Azure Portal.
Speaking of free SSL/TLS certificates for cloud-scale deployments: Letsencrypt offers cloud-scale provisioning of SSL/TLS certificates free of charge (with some restrictions). Find out more about Letsencrypt in action.
Gain insights into cyber security on AWS versus Azure
Monitoring of events relevant to cyber security was never easy. AWS and Azure seem intent on helping you to harness their machine learning prowess to do just that.
Inspect workloads
Wouldn’t it be nice to have the ability to automatically assess applications for vulnerabilities or deviations from best practices? Both AWS and Microsoft Azure offer an automated security assessment service. On AWS, it is called the AWS Inspector. On Microsoft Azure, you simply refer to the Security Center. Both services are agent-based, but only Azure offers automatic agent installation. By enabling data collection for your Azure resources you enable agent installation.
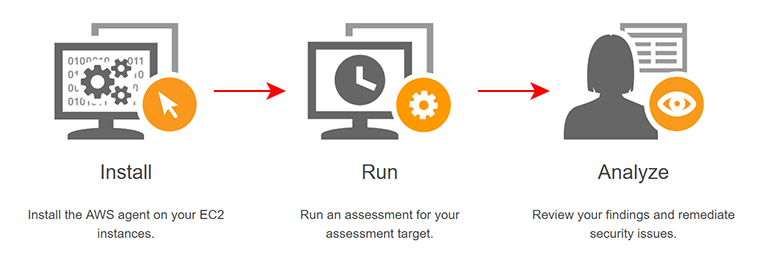
Amazon Inspector
Amazon Inspector allows you to analyze the behavior of your AWS EC2 instances (and possibly other resources in the future). The scope of analysis is called an assessment target. It is a collection of AWS resources that work together to fulfill one specific purpose. The Inspector uses so-called assessment templates to help you identify potential security issues. These require manual remediation.
The pricing for Amazon Inspector is calculated per agent per assessment (“agent-assessment”) per month. The AWS Inspector sends its alerts using the SNS service, so additional charges may apply. In terms of the visualization of actionable insights, export to CSV is all you get.
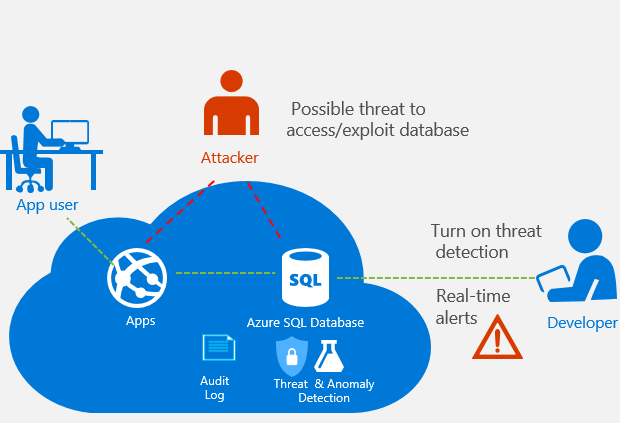
Azure Security Center
What AWS calls assessment templates, Azure refers to as policies. The scope of threat prevention and detection is broader than on AWS as of this writing. It covers Azure Virtual Machines, Firewalls, SQL Databases and Storage Disk. Azure Security Center integrates with Power BI, Microsoft’s set of business intelligence tools for interactive data visualizations (available in a free and a paid edition).
Analyze
With so many services sprouting up all over the AWS Console and Azure Portal, comprehensive advisory tools soon prove indispensable. In this department, AWS offers its Trusted Advisor. Microsoft called its equivalent the Azure Advisor. Both services provide analysis of cloud resource configuration and security settings for your environment.
Detect threats based on anomalies
Azure Advanced Threat Protection (ATP) by Microsoft can shield hybrid environments from multiple types of advanced targeted cyber attacks and insider threats—particularly those that focus on Microsoft’s technologies.
Microsoft pioneered the use of machine learning (ML) in threat detection with its Azure SQL Database Threat Detection service, an additional layer of security intelligence built into the Azure SQL Database service. The service keeps a watchful eye on user activities, learning and profiling. Based on the collected intelligence, it can detect anomalous database activities which may indicate unusual and potentially harmful attempts to access or exploit your databases — without you having to write code.
AWS followed in its rival’s footsteps with a cloud service called Amazon Macie, which it acquired from Harvest.AI(see below).
Classify data based on risk profile
Azure Information Protection (AIP) und Amazon Macie use machine learning to classify data and proactively implement protective measures without the need for human supervision.
With your permission, these services sniff around your infrastructure to discover sensitive data such as passwords. Azure Information Protection (AIP) suggests appropriate metadata for manual tagging by a user. It then deploys Azure Rights Management (Azure RMS) to apply encryption, identity, and authorization policies to data regardless of its eventual location.
Amazon Macie classifies data using machine learning. Based of this classification, the service applies risk ratings to the different types of content uncovered. Following this assessment, the service is then able to identify unusual access patterns that could indicate a security threat—and will alert you to it.
Macie currently supports around 70 types of data. These include Personally Identifiable Information (PII), Personal Health Information (PHI), regulatory documents, emails, source code, API keys and private keys. The service can automatically spot full names, addresses, credit card numbers, IPs, driver license IDs (U.S. only), social security numbers and birth dates.
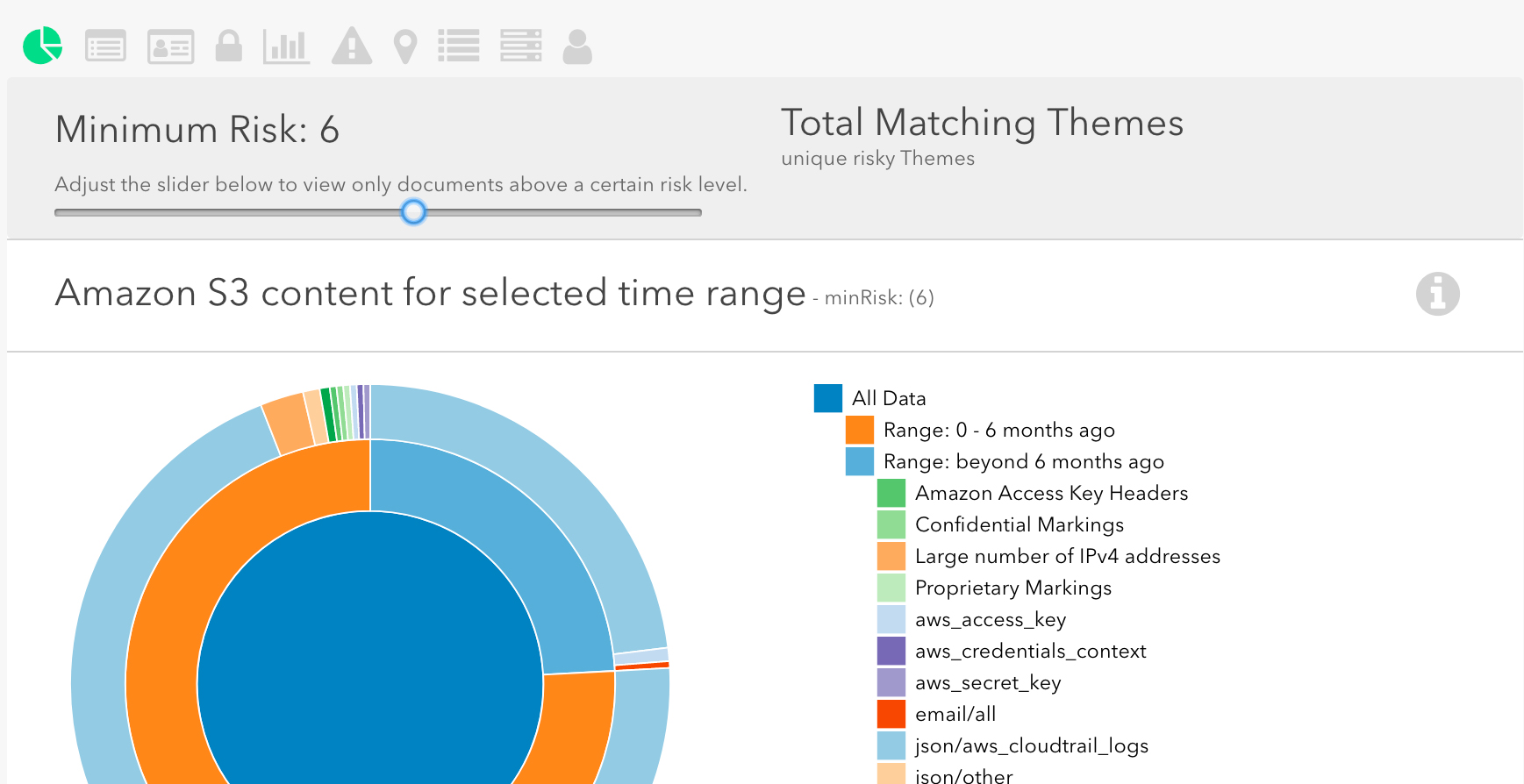
Amazon Macie can integrate with Security Information and Event Management (SIEM) services and Managed Security Service Provider (MSSP) solutions to help support various cyber security scenarios and compliance use cases.
Cyber defense on AWS and Microsoft Azure
When defending your cloud infrastructure against cyber attacks, an administrator can use all the help they can possibly get.
Defend against web exploits
When it comes to securing resources from unauthorized access, reducing outside exposure is the first order of the day. A firewall can come a long way to protect web applications from common web exploits. Quite predictably, AWS nicknamed its service Web Application Firewall. Microsoft was more creative: on Azure, look no further than the Application Gateway Web Application Firewall (currently in preview).
Shield from DDoS attacks
Massive distributed denial of service attacks (short: DDoS) require a sophisticated defense as the attackers keep abusing legitimately accessible resources while constantly shifting their tactics to elude countermeasures. AWS Shield helps you protect your resources from these kinds of threats. There is no equivalent offering on Microsoft Azure other than 3rd party software found in the Security section of the Azure Marketplace, which is a shame. DDoS attacks may not be very common, but they tend to be very expensive. Don’t expect prior notice before you get into the cross hairs!
Other noteworthy services
Other noteworthy services relevant to cyber security and compliance include managing multiple organizational cloud accounts and taking advantage of certifications that AWS and/or Microsoft may have acquired.
Azure Sphere: secure and power the intelligent edge
With the service Azure Sphere, Microsoft addresses the growing need in corporate IT to get a grip on edge devices.
Azure Sphere can manage IoT endpoint security, app downloads, authentication and attestation. The service uses Linux and a cloud-assisted security broker model.
Manage multiple cloud accounts
Working with multiple accounts poses its own set of risks. It requires a thoughtfiul security policy and role management. AWS offers a service dubbed AWS Organizations Subscription. Microsoft wants to subscribe you to something called the Azure Subscription and Service Management in addition to Azure RBAC (short for Role-Based Access Control).
Assure compliance by using others’ certifications
In terms of audits and certifications for the cloud services, the competition between AWS and Azure is nothing short of an arms race.
AWS Cloud Compliance provides an overview of assurance programs for finance, healthcare, government and others in place at AWS. Users can download access-controlled documents relevant to compliance and security by visiting AWS Artifact in the AWS Management Console. (Be prepared to sign an NDA agreement!) In addition, AWS discloses its general scope of certifications, including industry-specific compliance audits, in its AWS Certifications, Programs, Reports, and Third-Party Attestations whitepaper.
Microsoft celebrates Azure’s certification achievements as a compliance leader of the cloud pack. “In addition to the broadest compliance portfolio amongst enterprise cloud providers, Azure maintains the deepest coverage as measured by how many customer-facing services are in audit scope”, writes Alice Rison, Senior Director of Microsoft Azure. Audit reports for Microsoft Cloud Services (except those for Visual Studio Team Services) are generally available through the Service Trust Platform on Azure. Access requires, quite predictably, that you sign an NDA (online).
Leave a Reply