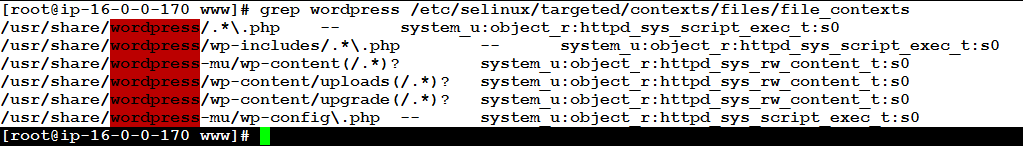
SELinux can be such a nuisance. In particular, if you have a newly created file system, you will need to add labels to it, also known as SELinux security contexts.
Cyber security, infotech
Filipe Martins Leave a Comment
SELinux can be such a nuisance. In particular, if you have a newly created file system, you will need to add labels to it, also known as SELinux security contexts.

Finding errors in a postfix log file is tedious work. The job gets even more complicated if you have to dig through old postfix log files which might no longer be relevant. logrotate comes to the rescue, but only if you configure it correctly. Here is how you can do it on Fedora.

Most of us have a love-hate relationship with SELinux.
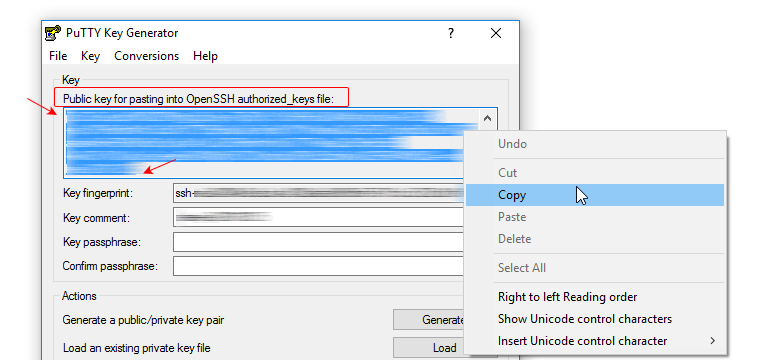
Your users want to access a web server instance as a staging or production environment for DevOps… They want access to the web server document root of the sites they manage. Your job is to maintain the integrity of the whole system in terms of cyber security.
If you happen to be running a web server on Linux—for example in EC2 on Amazon AWS—and need to provide site owners remote access in a secure and responsible manner, here is how to do it.

When updating MariaDB, the popular successor to MySQL, you may, once upon a time, hit a roadblock which you won’t be able to track down in the error log. Even though web visitors get to see the plain text complaint “Can’t connect to the database”, the MariaDB server will be running just fine. Silent errors should be reason enough to suspect SELinux, the oftentimes dreaded and despised but equally popular Security-Enhanced Linux kernel module.
©2022 CybrAnalytiqa OÜ