In light of documented TLS vulnerabilities and implementation bugs, understanding known attack vectors becomes a necessity.

Cyber security, infotech

In light of documented TLS vulnerabilities and implementation bugs, understanding known attack vectors becomes a necessity.
[Updated May 16, 2018] AWS and Microsoft, the two leaders in the race for the best cloud infrastructure, have recognized cyber security as a barrier of adoption. Cyber security professionals are weary of migrating workloads into public cloud environments as it may carry significant risks. Thus, Amazon and Microsoft have developed specialized services to help safeguard users’ cloud infrastructure and data.
This post discusses ways to mitigate cyber threats and launch a cyber defense on AWS and Azure.
“You know, if you have something really important, write it out and have it delivered by courier, the old-fashioned way. Because I’ll tell you what: No computer is safe (…) I don’t care what they say.”
President-Elect Donald Trump
In the waning days of the fading Obama presidency, plenty of questions surfaced about Russia’s involvement with the hacks of the DNC and election systems. Electronic evidence can be easily manipulated.
There is more to it than just electronic evidence.
Filipe Martins Leave a Comment
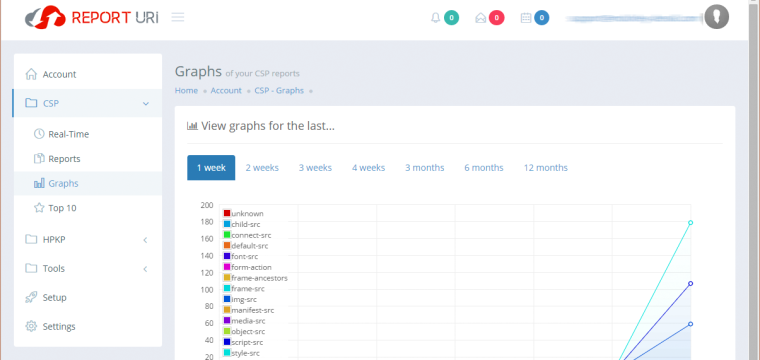
[Updated 2019-03-17] Are you wondering why some JavaScript code from external domains simply won’t execute on your website? The reason could be as simple as an overly restrictive Content Security Policy (CSP for short). This article explains how you can create a Content Security Policy that’s both protective and functional. It will help you to secure your web server from some types of cross-site request forgery (XSRF/CSRF/XFS), clickjacking and other code injection attacks.

The traditional perimeter-focused security model has outlived its active usefulness as evidenced by the never-ending array of security breaches that constantly push the envelope on our tolerance for administrative “malpractice” in IT.
From the various security breaches in the private sector that are by now too plentiful to enumerate, through the fingerprint-stained OPM disaster, to the recently leaked database of personally identifiable information on over 191 million registered voters (in other words: all of them): no vulnerability seems too obscure, no exploit too impractical, no hack too audacious for some keyboard-toting mercenary to take advantage of the collective naiveté–or is it sheer incompetence?–of those who are paid to protect and defend access to sensitive information. How in the world did these people get their jobs, how dare they draw a salary, and how can they sleep at night? And, even more importantly: are you, by any chance, one of them?
©2022 CybrAnalytiqa OÜ