Extracting domain names from email addresses with the help of regular expressions takes just a nanosecond once you have the formula. The formula is the key.
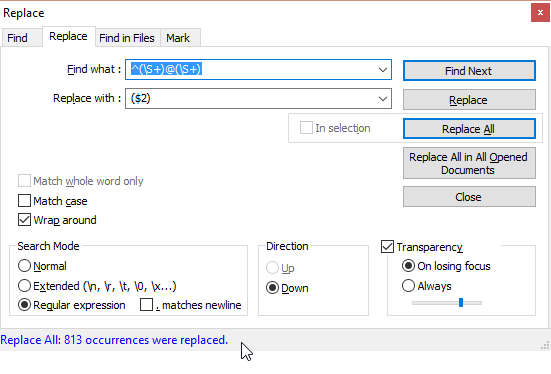
This is how you let your text editor find (and “understand”) each email address as two groups of characters separated by the @ symbol:
^(\S+)@(\S+)
This is how you perform the replacement, removing everything except for the domain name (as defined by the second group of characters in the regex above):
($2)
It’s that easy.
Practical Use Cases
One notable use case: Your email client may have collected untold amounts of email addresses from spammers. Now instead of blocking them on the client level (after delivery to your sorry inbox), you may want to block them at the mail server level. That’s easy enough (for example, you could be using smtpd sender restrictions in Postfix), but what if you wanted to block all senders from the offending domains? Exactly. You need to remove the user names in front of the @ sign, leaving only the domain names in the file. That’s where a regular expression can come in handy.
One more thing: how do you come up with a regular expression of your own? By using a really good RegEx editor like regex101.com and testing your regular expression on a sample of data.
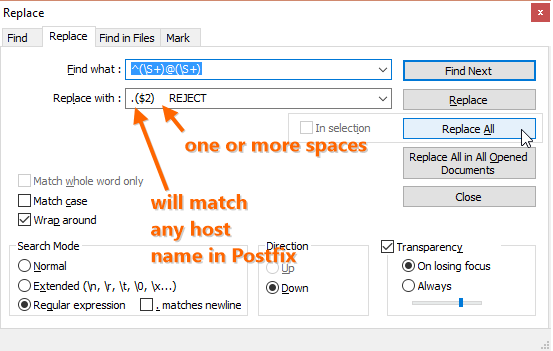
Assuming that you want to match any host name on each of the domains in your Postfix configuration and reject each message that matches the sender’s address, you need to prefix each of the domain names in your list with a dot, append a space and the REJECT directive.
Once this is done, you may end up with a list full of duplicates. You can sort it and remove the duplicates in Notepad++ using the module TextFX and the following commands:
- “TextFX > TextFX Tools > + Sort outputs only UNIQUE (at column) lines” activates the first option;
- “TextFX > TextFX Tools > + Sort ascending” activates the second option;
- “TextFX > TextFX Tools > + Sort lines case insensitive at column” performs the magic by sorting all lines and removing duplicates.
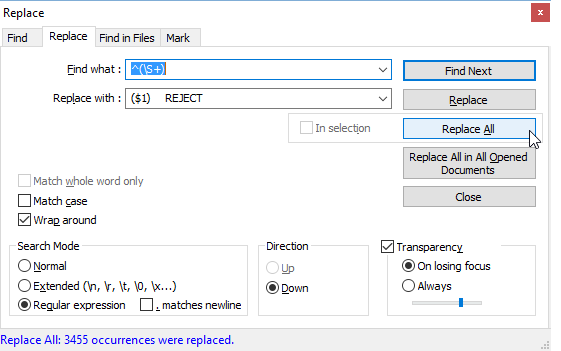
If you need to perform some other action, you can help yourself to another regular expression (just remember to pay attention to the character encoding in your file; different systems encode line breaks differently: LF on Linux/Unix, CR/LF on Windows and CR on OS X).
Now you can use the resulting list of spamming domains to feed Postfix smtpd client restrictions through this parameter:
smtpd_client_restrictions =
A word of caution, though, is in order: your email-address-list-turned-domain-list may include domain names of legitimate email service providers such as gmail.com or yahoo.com. As a result of this configuration, you would block all their users from communicating with your Postfix. This is bad for business. You may want to apply this technique only to slam-dunk cases of spamming domains, otherwise put smtpd sender restrictions in place.
Either method will take a huge workload off of your MX server.

Leave a Reply