Generating SSL certificates when Letsencrypt (what is Letsencrypt, who is behind it, and how the heck can you get started) is available for your system works in a breeze, but what if you need your certificates for a machine that won’t take Letsencrypt (for whatever reason)? It is still possible: you can either grab Letsencrypt from Git, or, for reasons of practicality… create a certificate signing request (CSR) on your target server, transfer it to your letsencrypt instance, generate the certificates you need, then transfer the generated files back to your target instance and install the certificates in your software.
Step 1. Adjust the DNS configuration for your target server (the one that needs the certificates)
Make sure that requests to the host names that need the certificates are being routed to the IP address of your target server via an A entry. Unless an A entry is in place, letsencrypt (on your other instance) will flat-out refuse to cooperate.
Step 2. Adjust openssl configuration on your target server (the one that needs the certificates)
On the target machine (that is, on the server that will be using the certificates), navigate to the openssl configuration file openssl.cnf located in:
cd /etc/pki/tls
Make a copy of it.
cp openssl.cnf openssl.cnf-original
Now open the original in a text editor of your choice. Enter these two lines:
[SAN] subjectAltName=DNS:domainname1.tld,DNS:host.domainname1.tld,DNS:host2.domainname2.tld
Make sure you replace the host names (domainname1.tld, etc.) with the host names that you want to generate your certificates for.
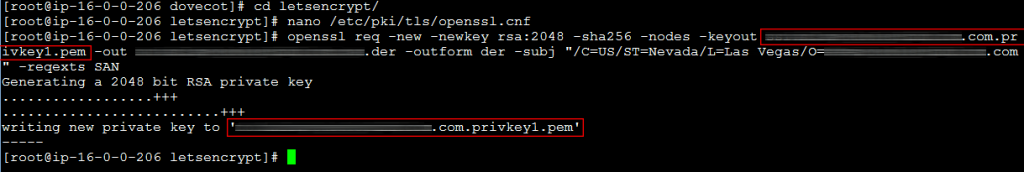
Step 3. Generate the certificate signing request on the server that will be using the certificates
On the target server (that’s the one that needs the certificates but can’t run letsencypt), generate the certificate signing request using the config file that you modified in Step 2 above:
openssl req -new -newkey rsa:2048 -sha256 -nodes -keyout filename.privkey1.pem -out filename.der -outform der -subj "/C=US/ST=Nevada/L=Las Vegas/O=domainname1.tld" -reqexts SAN
Adjust the parameters as needed, especially the country, state, city, and your domain name (entering incorrect information constitutes a breach of the Terms of Service of Letsencrypt, so no “test city” here!).
You should see a confirmation. Verify that openssl has generated two files:
a .pem private key and a .der encoded certificate signing request (CSR). Don’t bother converting them, letsencrypt will do just fine.
Step 4. Transfer the CSR .der file to your letsencrypt machine
Transfer the .der file to your letsencrypt machine. One way to do this is using rsync, another good option is FileZilla.
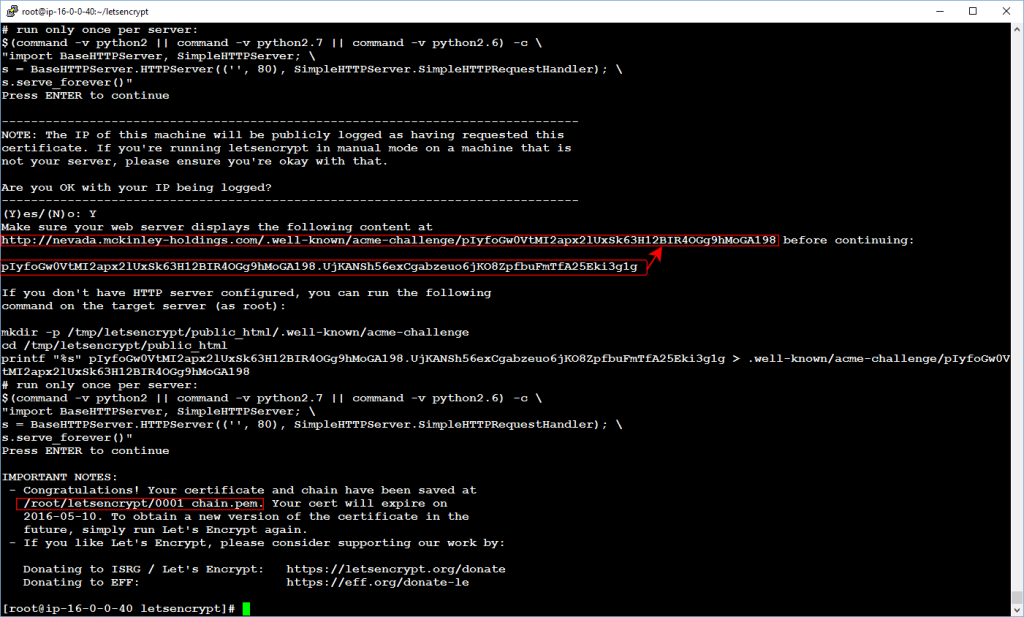
Step 5. Request your certificate files
On the letsencrypt machine, request your certificate files:
letsencrypt certonly --authenticator manual --server https://acme-v01.api.letsencrypt.org/directory --text --email your@emailaddress.com --csr host.domain.com.der
Your IP will be publicly logged as having requested the certificate.
In order to authenticate your server, follow the onscreen instructions. You can either save an authentication file to a web server directory and serve it via http, or run a Python script that the assistant provides, whichever seems more convenient. You should see a confirmation message announcing the path to your certificate chain.
Step 6. Transfer generated files back to the target server
Transfer generated files back to the target server and save them with 640 permissions. Configure your software (such as your mail server and your web server) to use the certificates, and don’t forget to renew them within 90 days!

Leave a Reply