A web service called Report URI can be a great help in creating an HTTP security policy that will protect your web application without compromising its functionality. Here is how to set it up to bolster your defenses against code injection attacks.
Code injection attacks pose a massive danger to any web application that’s exposed to the world. It literally takes minutes after a domain registration for the evildoers to come sniffing around. Chance are, they will keep coming back until the day they break in to vandalize your web application, hijack a user session or steal data some other way. By setting HTTP Security Headers, you can reasonably prevent code injection attacks in most cases (for more, read: Fixing your Web Server’s Security Headers: From Hall of Shame to Hall of Fame). A Content Security Policy header can effectively suppress code injection attacks.
There is no better way to define your content security headers than by using Report URI. Here is how to set it up.
The service allows you to obtain an report-uri endpoint for use with the directive Content-Security-Policy-Report-Only to log security incidents that violate your security policy as a result of user interactions with your web application.
Step 1. Obtain an report-uri endpoint
In your web browser, navigate to
https://report-uri.com/
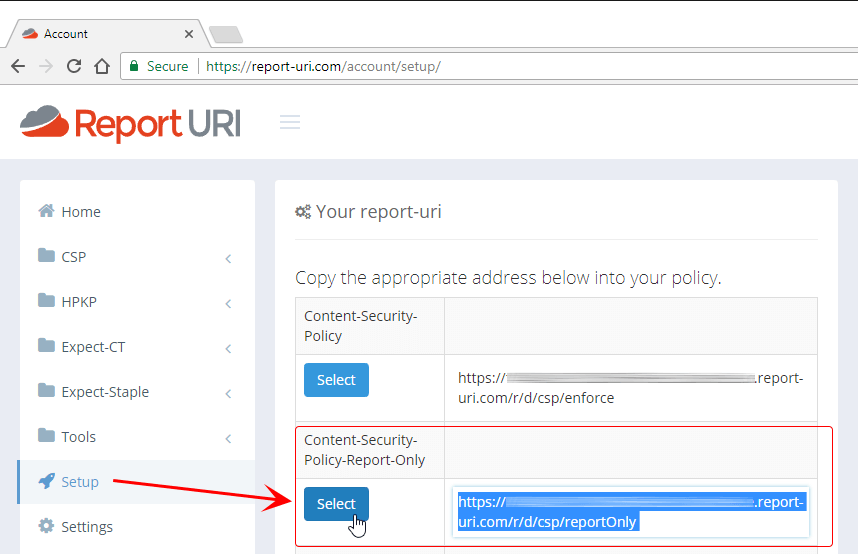
Sign-in to your account and head over to the Setup section. From the list of report-uri endpoints, select the address titled Content-Security-Policy-Report-Only and copy it to your clipboard.
Next, you will want to enter this address into your web server configuration for your domain, but before the service will start collecting information, you have to do one more thing: define the domains to collect reports for.
Step 2. Enter eligible domains to collect security incident reports for
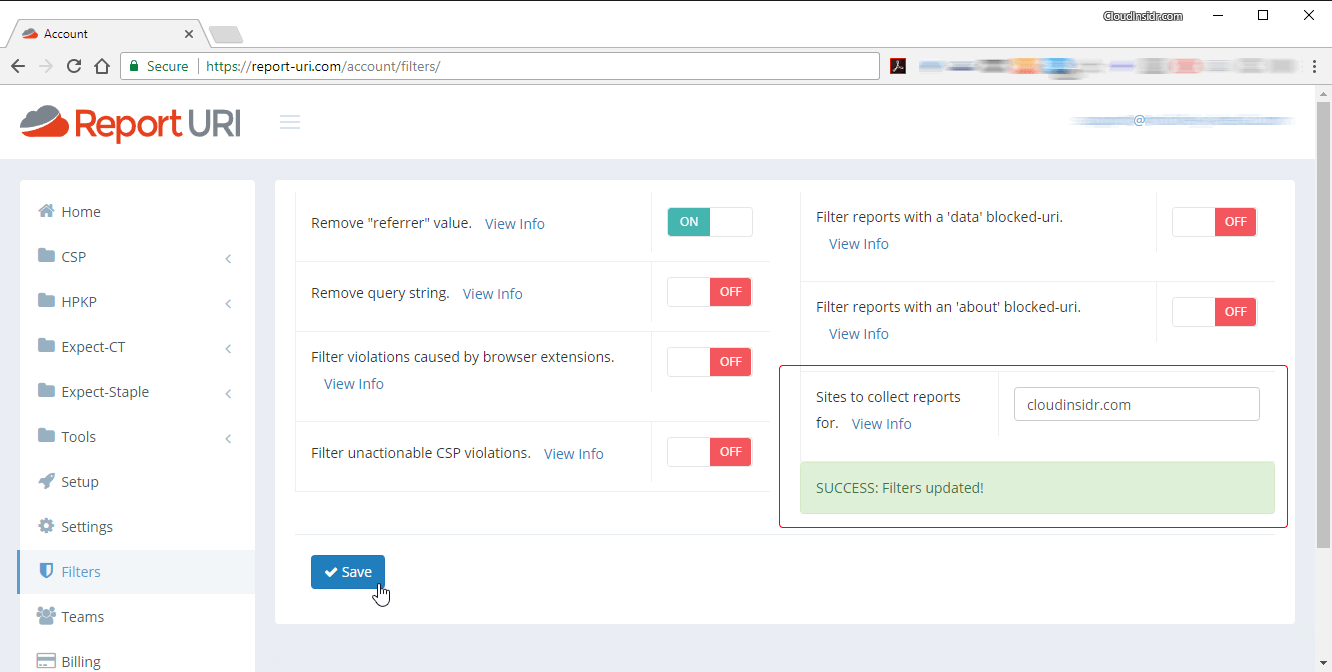
Navigate to the Filters section. Enter all the domains you want to keep an eye on into the field “Sites to collect reports for”, without the scheme, separated by a space:
domain1.tld domain2.tld domain3.tld
The service Report URI is now ready to collect reports—but is your web server ready to ask user agents to submit them?
Step 3. Configure your web server to use the report-uri endpoint
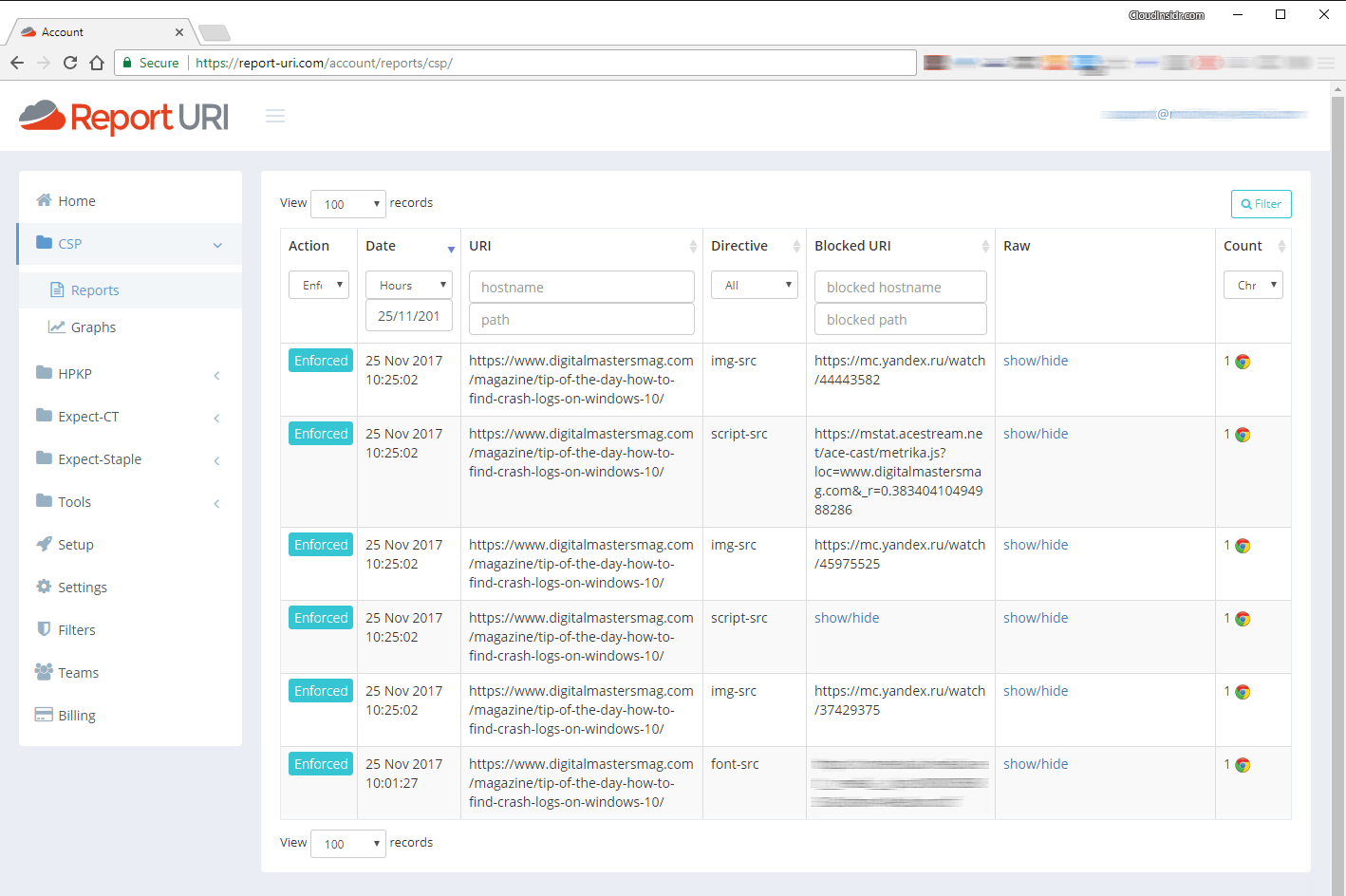
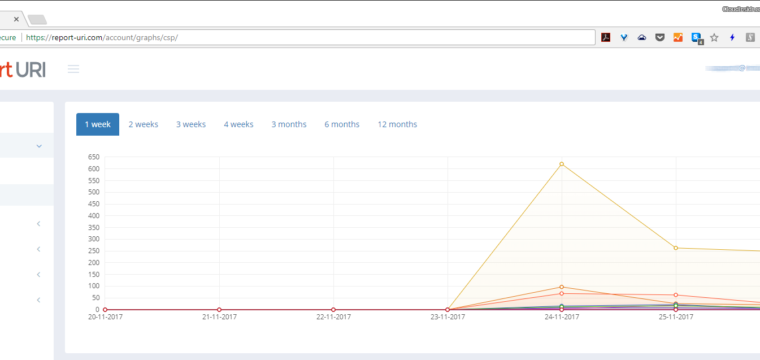
Setting up your web server to use your report-uri endpoint involvs adding a directive to your web server configuration file (see How to Create a Content Security Policy to Protect Your Web Application against XSRF/CSRF/XFS, Clickjacking and Other Code Injection Attacks for details). After a brief delay, the reports of any incidents that violate your current polity should begin streaming in. You will find them in the CSP section of your Report URI account.
Step 4. Analyze Report-URI incidents
Don’t just allow the reports to roll in, you need to take action.
Here is an example of an attempted code injection attack on our sister site Digital Masters Magazine. Attackers attempted to collect data using a 1 px image; the attempt failed thanks to the Content Security Policy in place.
Leave a Reply